Here are the slides from my FasTrak talk and a short summary of my findings. I’m hoping what I’ve found can help officials improve the security and privacy of these systems.
FasTrak and related toll collection systems have been around since the mid-90’s. I started looking at them because I had never signed up due to privacy concerns. However, while the underlying Title 21 standard is public, I couldn’t find any details about the internal workings of the system or any security measures. I bought a few transponders and took them apart to find out.
Besides support for the standard messages, I found no encryption. So it’s easy for an attacker to use a simple RFID reader to collect transponder IDs from cars in a parking lot, then replay them to bill tolls to the real owners. By only using each stolen ID once, it would be difficult to track them down.
Even more surprising, I found support for a lot of proprietary messages that go far beyond toll collection. By sending a few packets, an attacker can activate a hidden “update mode” that allows the ID to be wiped or overwritten with a different one. This goes against claims that the transponder is “read-only” and “there is no memory to write anything to”.
The ability to clone and/or overwrite IDs over-the-air calls into question the admissibility of FasTrak logs as evidence. They get regular subpoenas for these logs, and I wonder how many innocent people were convicted based on the claimed reliability of this system. A non-technical attack is to steal a transponder from the victim and surrepititiously plant it in someone else’s car, creating fraudulent evidence that the victim was somewhere they were not.
Also, the 511.org service creates a massive collection of data, logging every section of freeway traveled by each car that has a transponder. FasTrak has told a reporter (story) that this data is discarded after 24 hours but I can find no written evidence of this. Since all this system does is generate statistics of average travel times, it could be significantly reduced from its current form. Instead of querying and logging all cars, it could randomly sample cars so only 1 out of every 100 were used. Each record could be discarded after 10 minutes or so since the readers are located approximately at each freeway exit. A car that was logged at one sign but not the next probably exited.
This updated system would still achieve the stated goals while reducing the chances for a privacy compromise. It also would only require changing the server software, not the readers or transponders.
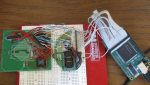
I’m working on an add-on “privacy kit” to retrofit transponders. It consists of a timer circuit and activation button, similar to a garage door opener. It keeps the transponder powered off except for a minute or so after the user presses the button. This protects the user from privacy exposure (except while paying tolls) and cloning or overwrite attacks. The downside is it would require technical skills to attach to the transponder. However, newer models are coming out that have an open battery bay, making it easy to add this privacy kit.
I hope to release schematics free of charge and create a kit that would be available at no profit to myself. Hopefully this will convince transponder vendors to add an opt-out capability into future designs.
Transit agencies interested in more details on my research can contact me here.
Interesting stuff
That was a nice set of slides, very interesting. Makes me feel “”real”” safe taking my toll road to work every day.
is this happening in others states? IL?
Thanks you for posting this, Nate!
I have a question though: Does that bag that comes with a transponder give you any sort of protection whatsoever? How about a lead-lined film bag some photographers used to protect film from X-ray machines at airports (My grandfather used to use it, and I have it at home.)?
fred: IL uses I-Pass, east coast uses E-ZPass. While they share the same frequency band as Fastrak, the protocol is different. However, they should definitely be reviewed even though they claim to have some sort of encryption. I doubt they are significantly stronger.
NateJPeck: the bag they supply with the transponder is a normal computer anti-static bag. It is enough to block the signal since it is pretty weak.
I am not and have never been a Fastrak customer. I received a letter titled SECOND NOTICE – DELINQUENT TOLL EVASION VIOLAATION. It claimes that 15 months ago, I went thru a fastrak lane on the Bay Bridge (no. 20) without paying or having a transponder. I have been unable to find any info about who Fastrak is (a private company, rught?),where they are located, or any tech info about how the system works and doesn’t work. I Can not believe I would drive thru a toll booth with out stopping to pay my toll, nor can I imagine gettting a FIRST Notice about this mattter and forgetting as much. So, if you are not too busy and this is your area of expertise, can you respond with some information? I have requested an administrative review, but is seems slanted towards fastrak.
sincerely, james Mead
James, you should ask for a copy of the photo they took of your license plate. It’s possible it was misread.
A suggestion for your privacy kit idea: add an LED to tell the user that yes, the transponder is active. Make it solid except the last five seconds when it flashes once per second, so the user can hit the button to reset the timer before it expires in case it takes longer than expected to reach the toll booth.
I’m in the process of disputing a FasTrak charge that is either an error in their system or the result of a clone of my transponder. It is amazing how totally obstinate (and at time rude) they can be. It’s only $5 but I refuse to be taken advantage of. I find it interesting that they take photos of license plates for cars that pass FasTrak lanes without a transponder – but they do not take photos of cars that do have a transponder. In my case they could easily see that the vehicle using my transponder code was not my vehicle. And in the case mentioned above where a cloner grabs lots of codes and only uses them once each they could easily find that a particular license plate number was associated with a large number of disputed charges all from different transponder codes. But then, they don’t really care, yet…
Mike, sorry to hear that. The EZPass system on the east coast does take pictures of vehicles with valid transponders so it is possible FasTrak could do that as well. I continue to hope they will address all these issues before it becomes a big problem.
I finally got my refund from FasTrak so I’m a little less inclined to crusade for improvements to their system. But the whole experience was quite eye opening.
First, off, sometimes it’s acceptable to decide that the cost of a problem is still cheaper than the solution. FasTrak could decide that the way to deal with clones is to credit anybody who calls and disputes a charge, as I did. People would try to abuse this, but you simply don’t let any one person get away with more than one, maybe two disputes. But, if that’s a conscious decision, you have to push it to the lowest level support reps. It could have cost them $10 – the $5 credit plus $5 (being very generous) for the time required for one dispute phone call. But, my dispute probably cost FasTrak a couple of hundred dollars and I was prepared to make it far more expensive. I called them probably 6 or 8 times, talked to a manager, wrote to them, etc. What a bunch of maroons…
The other eye opening thing was how totally technologically illiterate their customer service staff is. We see it all the time in countless other support operations where untrained people working from a script force us to waste huge amounts of time trying solutions we know won’t work. But we also know how glorious it is when we get the one person on the line who actually understands the technology he/she supports and the problem is solved quickly and painlessly. In my last conversation with FasTrak they offered to refund my $5 if I would send my transponder in (at my expense…) for testing so they could find out what was wrong with it. Think about that for a sec – it was in my car, in my driveway, 60 miles from the GG bridge at the moment they say I drove across the bridge with it. And they think some defect in the transponder itself caused the GG bridge equipment to think it saw my transponder? It could be this was just another hoop to make me jump through in their misguided effort to save $5 by spending hundreds talking to me on the phone and making me send a written dispute and making me ship them the transponder – maybe the next step would have been a request to bring my car in for inspection. Or it could be that they know more about clones than they admit and wanted my transponder out of the system since some cloner somewhere apparently has grabbed my ID. But, the simplest answer being the correct one, the truth is that the vast majority of people who work for FasTak don’t have a frigging clue how the damn thing works! Oh, what a better world it would be if more companies were more concerned with educating their workers.
I hope they realize how bad it will all get if they don’t improve their fraud prevention act. And I hope they’re silently working on something. But, based on my experience so far, they’re just incompetent.
Nice, Nate.
I have always been ticked off by the letter that came with mine claiming it couldn’t be used to track me.
How many possible transponder IDs are there? (There are only 1 billion SSNs!) I.e. can an algorithm come up with transponder IDs that are valid frequently enough to be useful?
PS I guessed right! http://commons.wikimedia.org/wiki/File:Roadside_antennae.jpg
I’d have to dig up my notes to see. The address space is subdivided by CA agency, and I remember it was pretty small once you got down to it. I’d guess somewhere around 24 bits (16 million) usable addresses.